Are you tired of juggling numerous login credentials for different cloud platforms? Frustrated with the time-consuming process of resetting passwords and updating security measures? Well, we have good news for you! Cloud Key Login has arrived, offering a seamless, secure, and hassle-free way to manage all your cloud accounts with just one login credential. In today’s fast-paced digital world, the ability to efficiently manage multiple cloud accounts is essential, making Cloud Key Login a game-changer for individuals and businesses alike. So, let’s dive into the details and explore how this technology can revolutionize your cloud experience.
How to Cloud Key Login
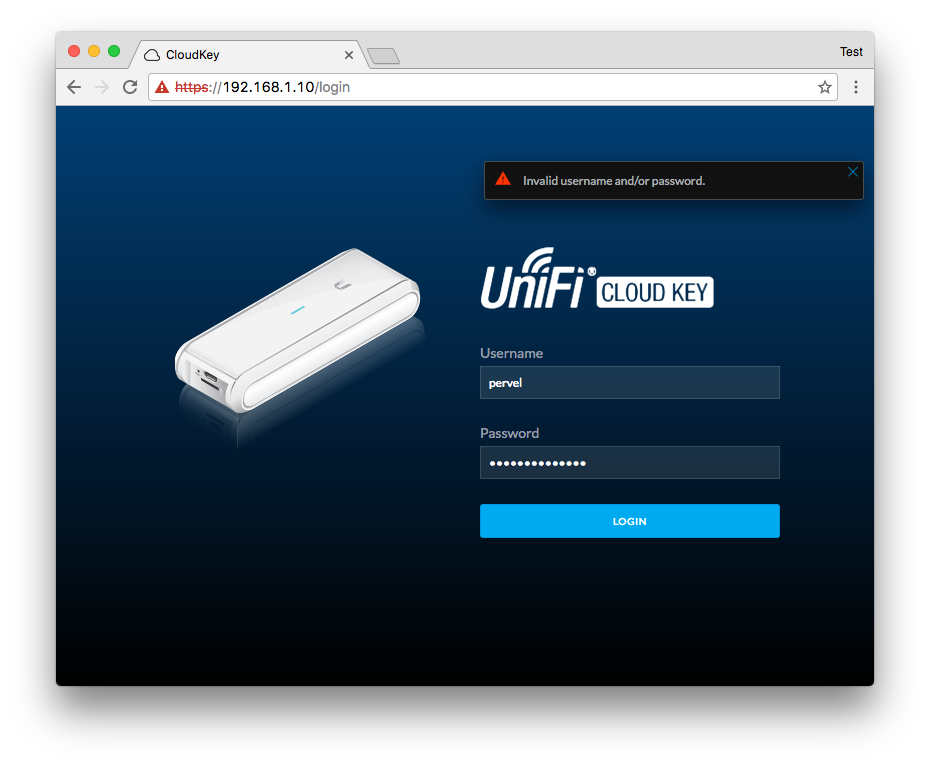
1. Open your web browser and go to the login page for your Cloud Key.
2. Enter your username and password into the appropriate fields.
3. Click the “Log In” button to access your Cloud Key account.
What to do if you Forgot Password or Username
If you forgot your password or username for your Cloud Key account, follow these steps to reset your credentials:
1. Go to the login page for your Cloud Key.
2. Click the “Forgot Password” or “Forgot Username” link, depending on which information you need to retrieve.
3. Follow the on-screen instructions to provide the necessary information to verify your identity.
4. Once your identity is confirmed, you’ll receive an email with instructions on how to reset your password or retrieve your username.
If you are still having trouble accessing your Cloud Key account, contact customer support for additional assistance.
Cloud Key Management
Cloud Key Management refers to the process of managing access to cloud-based applications and services. This is a critical aspect of modern IT security, as many organizations rely heavily on cloud services for their day-to-day operations. Cloud Key Management typically involves the use of secure authentication mechanisms to grant users access to the appropriate services and data, while protecting against unauthorized access and data breaches.
Cloud Security
Cloud Security is a broad term that encompasses a range of strategies and technologies designed to protect cloud-based data and applications. This includes everything from network-level security measures like firewalls and intrusion detection/prevention systems, to identity and access management solutions, data encryption, and more. The goal of cloud security is to provide a secure and reliable environment for businesses and individuals to store and access their data and applications, without fear of data breaches, cyber attacks, or other threats.
Multi-Factor Authentication
Multi-Factor Authentication (MFA) is a security mechanism that requires users to provide two or more forms of authentication in order to gain access to a system or service. This can include things like passwords or PIN codes, as well as biometric measures like fingerprints or facial recognition. MFA is an effective way to protect against unauthorized access and data breaches, as it makes it much more difficult for attackers to gain access to sensitive data or applications.
Single Sign-On
Single Sign-On (SSO) is a solution that allows users to access multiple applications and services with a single set of login credentials. This eliminates the need for users to remember multiple passwords or login credentials, and makes it easier for IT administrators to manage access to various applications and services. SSO is often used in conjunction with cloud services, as it allows users to seamlessly switch between different applications and services without needing to log in and out of each separately.
Identity and Access Management
Identity and Access Management (IAM) is a set of policies, procedures, and tools that allow organizations to manage user access to applications and services. This includes everything from creating user accounts and managing passwords, to defining roles and permissions, and monitoring user activity. IAM is an important part of cloud security, as it helps to ensure that only authorized users are able to access sensitive data and applications.
FAQs About Cloud Key Login
1. What is a Cloud Key?
A Cloud Key is a small device used to manage UniFi network devices, including switches, access points, and security gateways. It connects to the cloud to provide remote management and monitoring capabilities.
2. How do I log in to my Cloud Key?
To log in to your Cloud Key, you will need to enter the device’s IP address into your web browser. This should take you to the Cloud Key’s admin login page, where you can enter your username and password.
3. What if I forget my Cloud Key admin password?
If you forget your Cloud Key admin password, you can reset it by physically resetting the device. To do this, press and hold the reset button on the Cloud Key for around 10 seconds. This should reset the device to its default settings, including the default admin username and password.
4. How do I connect my Cloud Key to the internet?
To connect your Cloud Key to the internet, you will need to connect it to your network using an Ethernet cable. Once connected, you should be able to access the device’s admin interface through your web browser.
5. What can I do with my Cloud Key once I’m logged in?
Once logged in to your Cloud Key, you can manage and monitor your UniFi network devices, configure network settings, and view analytics and performance data. You can also remotely access your network from anywhere with an internet connection using the UniFi app on your mobile device.
6. Can I use my Cloud Key with other network devices?
Yes, you can use your Cloud Key with a wide range of UniFi network devices, including switches, access points, and security gateways. It can also integrate with other third-party devices using APIs and custom scripts.
Conclusion
In conclusion, accessing your cloud environment through a cloud key login is a secure and efficient way of managing your resources. It provides an additional layer of security while simplifying the process of logging in to your cloud platform. However, businesses must take precautionary measures by choosing reliable vendors and implementing security protocols to prevent security breaches and data loss.
In addition, cloud key login also represents a larger trend in technology towards simplifying authentication and access management. As our world becomes increasingly digitized, ensuring secure access is becoming more important than ever before. Cloud key login is just one piece of the puzzle as we continue to develop new technologies to protect our data and digital identity.
In the end, the key takeaway is that businesses must stay informed about the latest security trends and advancements in technology to protect themselves and their customers. By doing so, they can ensure their access management practices are secure, reliable, and up-to-date. It is only by staying ahead of the curve that we can guarantee the safety and security of our digital world.